Learn more about our unique approach
At Thales, we believe strong authentication should work for you—not against you. Passwordless 360° replaces outdated credentials with secure, user-friendly options that scale. Wherever you are in your journey, this approach helps you reduce risk, remove friction, and meet your organization’s access goals.
Security & Risk
Strengthen your security posture with phishing-resistant login methods, align with Zero Trust principles, and meet global compliance mandates like GDPR, DPDP, and NIS2—all while gaining full control over who accesses what.
Identity Operations
Simplify authentication management with a flexible framework that supports passkeys, FIDO2, and smart cards—built to work across legacy, cloud, and hybrid environments with fast deployment and full admin control.
Business Impact
Improve workforce productivity, reduce support costs tied to password resets, and deliver seamless, secure access experiences that scale across teams, devices, and regions—without increasing complexity.
No matter your user group, business model, or security challenge, we’ve got the perfect starting point to help you go passwordless with confidence.
Passwords create friction, invite risk, and frustrate users. Passkeys solve for all three — delivering faster logins, stronger security, and a consistent experience across devices and platforms. Whether you need high-assurance hardware, smooth customer access, or scalable enterprise solutions, our approach supports it all — so you can choose what fits, where it fits.
These days, most “Passwordless” strategies only solve part of the password problem. Our unique 360° approach brings everything together – biometrics, passkeys, hardware tokens, and adaptive risk signals – to deliver phishing resistant, standards-based authentication for every identity you manage. Stream the webinar series now and start building a stronger, smarter and truly passwordless authentication strategy.

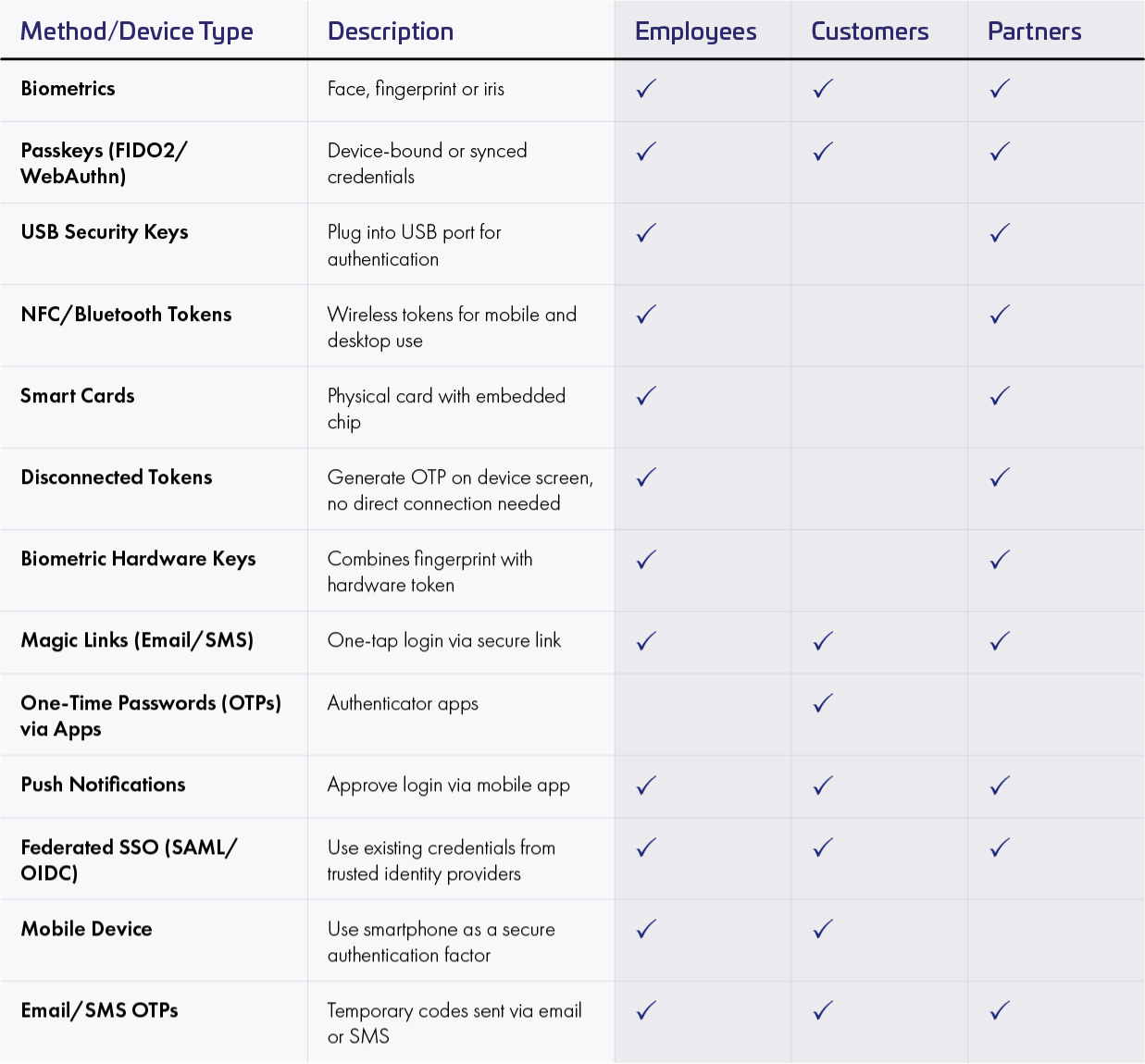
Passwordless authentication is an identity verification method that eliminates the need for traditional passwords by using secure, user-friendly alternatives like biometrics (e.g., fingerprint or facial recognition), hardware security keys, and possession-based factors. This minimizes the attack surface, making it exponentially more difficult for malicious actors to gain unauthorized access.
Traditional passwords are no longer effective — they're vulnerable to attacks and frustrating for users. Thales Data Threat Report shows that 31% of cloud data breaches stem from human error, and 17% are due to missing MFA on privileged accounts.
Consumers also feel the pain: 31% cite password resets as a top online frustration, and 17% have abandoned a brand over forgotten passwords. Organizations must move toward passwordless authentication — not just to reduce risk, but to improve user experience and protect brand loyalty.
Aside from being the weakest link in the cybersecurity chain, passwords are incredibly tricky for employees and administrators to manage. Just imagine the costs and productivity gains by eliminating the #1 reason for IT support calls: password resets.
Implementing passwordless authentication can lead to noticeable benefits within months for organizations, including fewer account takeovers, improved efficiency, and fewer headaches for administrative teams. Organizations can reduce costs associated with password resets, help desk support, and credential management.
Passwordless methods also improve the user experience for consumers, partners, and employees by delivering a seamless, frustration-free login experience.
The process typically involves the following steps for a passwordless login.
1. A user initiates the authentication process, such as attempting to log in to an application or service.
2. Instead of entering a password, the user is prompted to provide an alternative authentication factor.
3. The user responds with the requested factor, such as a biometric scan, a one-time code from a mobile app, a passkey or a hardware token.
4. The authentication system verifies the provided factor against the user's registered credentials.
5. Upon successful verification, the user is granted access to the desired application or service.
Hardware USB Tokens and smart cards are physical devices that employees can simply plug in to their laptop or tap to their mobile phone to authenticate themselves. Smart cards can combine physical access and digital access making them a reliable choice for high-security working environments.
The new generation of hardware authenticators support the modern FIDO standard (Fast Identity Online) and offers the best defense against phishing attacks and Man in The Middle Attacks.
Software authenticators are convenient solutions that help keep your accounts safe without needing extra devices. That means employees can just use an app on their phone. When they try to log in, the app sends you a notification that you just tap to approve, while temporary or frontline workers use web and pattern-based authentication to access medium sensitive resources.